Debugging Is Mostly Thinking, Not Commands
Debugging Isn’t the Problem. The Assumption Is.

Diving into Cloud and DevOps like a kid who learned cycling yesterday and signed up for a race today. I break things, read error logs like bedtime stories, and slowly figure out how not to repeat the same mistakes. If you enjoy honest tech journeys with a bit of humor, you’ll fit right in.
I remember staring at my screen late one night, trying to get a simple Docker container running on my local machine. It was part of this beginner DevOps project I’d set up—a basic web app that should have deployed without fuss. But it wouldn’t start. The logs spat out errors about ports and permissions, and I kept typing commands like docker logs and docker ps, hoping something would click.
At first, it felt like a puzzle I could solve with enough trial and error. I’d Google the error messages, copy-paste fixes from Stack Overflow, and rerun everything. But nothing stuck. The container would crash again, and I’d feel that familiar frustration building. It wasn’t just the code; it was me, wondering if I was cut out for this Cloud stuff.
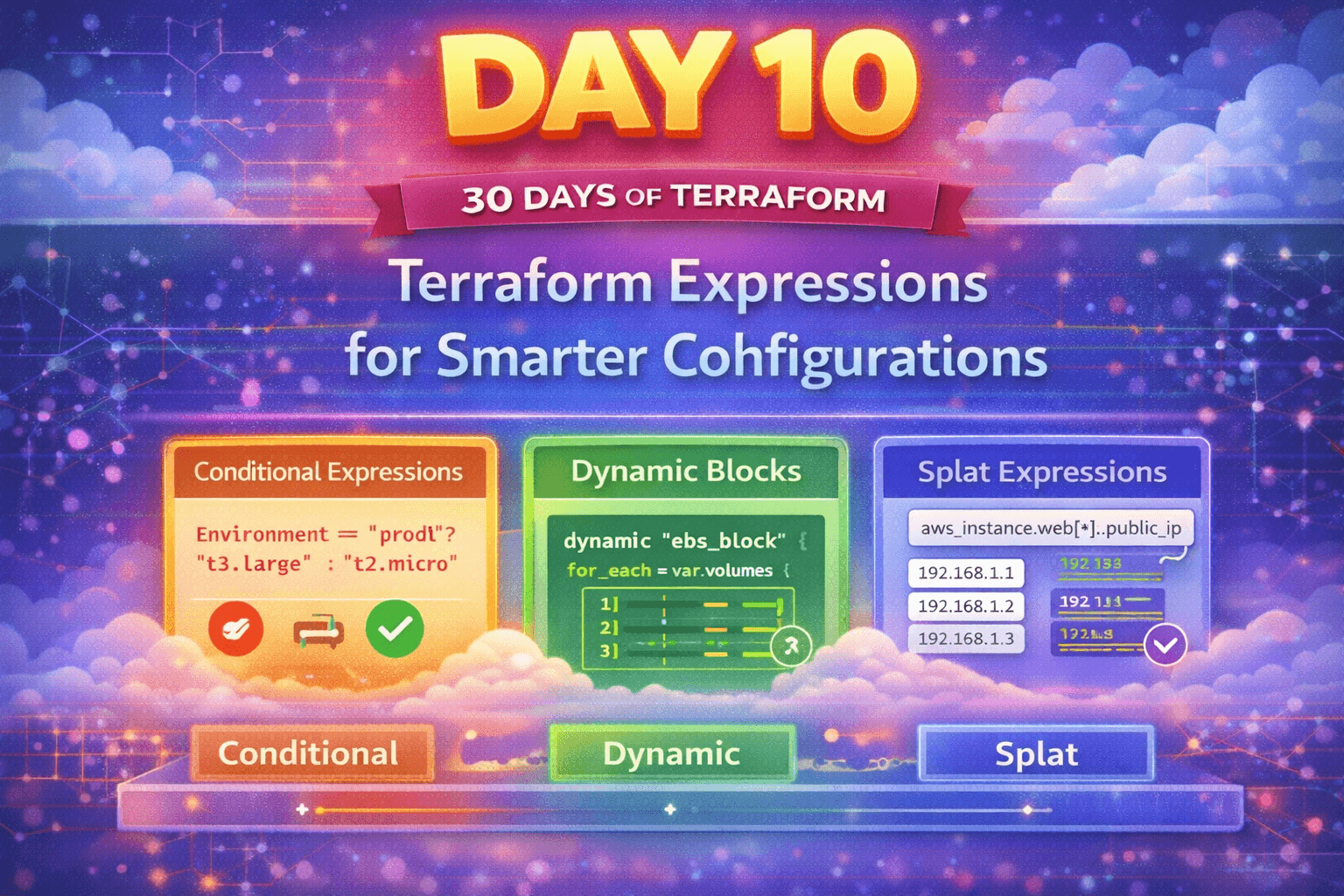
This happens a lot when you’re starting out in DevOps. You think the tools are the barrier—learning Kubernetes or Terraform seems daunting—but really, it’s the moments when things break that test you. And that’s where debugging comes in, or at least where I thought it did.
My Initial Belief About Debugging
I used to see debugging as a toolkit. Grab the right command, point it at the problem, and watch it resolve. In my mind, it was like being a mechanic: diagnose with kubectl describe or aws ec2 describe-instances, then fix with a tweak here or there. It made sense because that’s how tutorials present it. They say, “Run this to check logs,” or “Use that flag to inspect resources.”
I assumed that with enough practice, I’d memorize these commands and become efficient. Why wouldn’t I? In programming bootcamps, debugging is often reduced to breakpoints and print statements. Extending that to Cloud and DevOps felt logical—scale it up to infrastructure, but the process stays the same.
It felt reasonable because early successes reinforced it. When a script failed due to a missing environment variable, echo $VAR revealed the issue quickly. I’d pat myself on the back, thinking, See? Commands are key.
Where It Started Breaking
But then came this one deployment hiccup that wouldn’t budge. I was experimenting with a CI/CD pipeline on GitHub Actions, pushing code to an AWS ECR repository, then pulling it into an EC2 instance. Simple in theory. The build passed, the push succeeded, but the container on EC2 kept failing with a vague “permission denied” error.
I hammered away with commands: aws ecr describe-repositories, docker pull, sudo chmod on files. Nothing. The error persisted, mocking me. I even restarted the instance, thinking maybe it was a transient glitch. Hours slipped by, and I got confused—why weren’t the tools working?
The confusion deepened when I realized I was looping. I’d try a fix, fail, search for similar issues, apply another command, and repeat. It felt like chasing shadows. That’s when doubt crept in: Am I missing some advanced flag? Or is this just how DevOps is—endless firefighting?
Slowing Down and Thinking
Eventually, I stopped typing. I closed my terminal and just sat there, staring at the error message: “Error response from daemon: unauthorized: authentication required.” It was an auth issue, but I’d already checked my AWS credentials with aws configure list. They looked fine.
This is where I got stuck, but also where I started to shift. Instead of more commands, I asked myself basic questions. What assumptions was I making? I assumed the credentials were propagating correctly from my local setup to the EC2 instance. But why? Because I’d set them up once and they worked before.
I jotted down what I knew:
Local pull worked fine.
ECR policy allowed public pulls, but wait, was it public? No, I’d set it private.
Instance role—did it have the right IAM permissions?
Step by step, I reasoned through the flow. The pipeline pushes to ECR using my personal access keys, but the EC2 pulls using its instance profile. Were they synced? I hadn’t explicitly attached the ECR read policy to the instance role.
It wasn’t a command that revealed this; it was tracing the mental model of how AWS auth works. I recalled from a video that instance roles are separate from user credentials. So, I visualized the chain: code commit → GitHub Actions (with secrets) → ECR push → EC2 pull (via role).
What the System Was Actually Doing
The system wasn’t broken; it was following rules I’d overlooked. ECR repositories default to private, requiring specific IAM policies for access. My instance role had basic EC2 permissions but nothing for ECR. So, when Docker tried to pull, it hit an auth wall—not because of bad commands, but because the identity wasn’t authorized.
In plain terms, it’s like trying to enter a locked building with the wrong key card. You can jiggle the handle (run commands) all day, but without questioning if you have access at all, you’re stuck outside. The error message was a symptom, not the cause. The real behavior was AWS enforcing least-privilege security, which is great in theory but invisible until you think about identities separately from actions.
I avoided diving into jargon here, but terms like “IAM role” popped up naturally in my head because they’re how Cloud systems think about trust. It’s not magic; it’s layered checks.
The Turning Point
What finally worked was simple, but it came from that pause. I logged into the AWS console—not to run commands, but to visually inspect the instance role. Sure enough, no ECR policy attached. I added AmazonEC2ContainerRegistryReadOnly, saved, and tried the pull again. It worked.
Why did it work? Because I addressed the assumption, not the surface error. The commands were secondary; I could have used CLI to attach the policy (aws iam attach-role-policy), but the insight was in realizing the mismatch between push and pull identities. That click happened when I drew a quick diagram on paper—arrows from GitHub to ECR to EC2, with question marks on the auth steps.
It wasn’t triumphant; it was relieving. And partial—I still wondered about best practices, like using temporary credentials. But it moved me forward.
What This Taught Me
Assumptions hide in the setup: I learned that early configurations, like roles and policies, often cause downstream failures. It’s not about the debug command; it’s questioning if the foundation is solid.
Thinking builds a map: By slowing down, I started seeing DevOps as interconnected systems, not isolated tools. Each piece affects others, and debugging is redrawing that map when it doesn’t match reality.
Confusion is a signal: Getting stuck isn’t failure; it’s a prompt to step back. Rushing with commands often deepens the hole, while reflection uncovers the why.
Simplicity over complexity: The fix was basic, but it required peeling away my rushed mindset. This makes me approach new setups with more caution now.
In the end, debugging in Cloud and DevOps isn’t about mastering a list of commands. It’s about cultivating patience to think through the invisible layers. I’m still a beginner, making plenty of mistakes, but these moments remind me that understanding grows from reflection, not speed. Next time something breaks, I’ll try to remember: pause first, assume less. What hidden assumption might be tripping you up right now?